HashiCorp Vault Introduces Specialized Security Controls for AI Agents
The Challenge of Securing Autonomous AI Agents
Traditional identity and access management (IAM) systems were built for predictable, deterministic users and workflows. However, the rise of agentic AI introduces autonomous, non-deterministic actors that operate with far less predictability. These AI agents require a fundamentally different authorization model—one that blends identity, delegation, runtime policy evaluation, and ephemeral permissions. Simply granting broad access is no longer sufficient; each request must be tightly scoped to the agent's identity and the specific transaction context, with temporary rights that expire automatically.
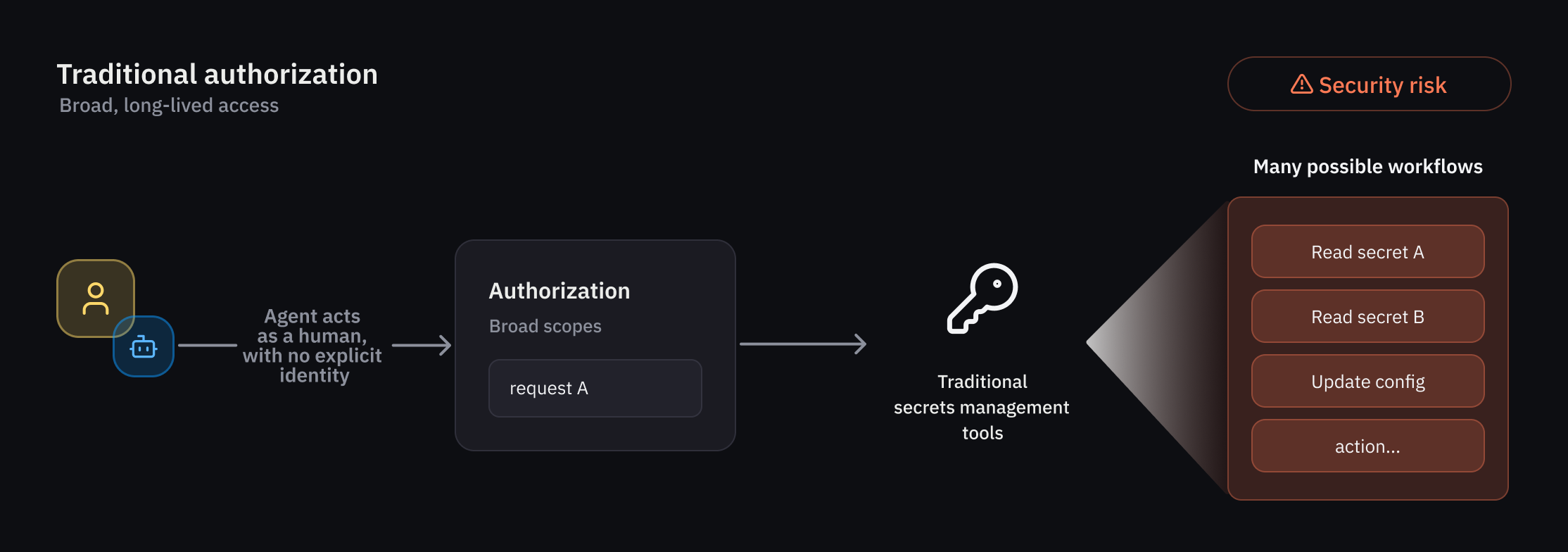
Why Traditional IAM Falls Short
As organizations deploy AI agents across their environments, HashiCorp Vault customers increasingly demand new identity and security controls tailored for autonomous systems. Key requirements include:
- The ability to enforce guardrails for agents that behave less predictably than humans or traditional non-human identities (NHIs).
- Fine-grained authorization that can be evaluated at runtime and scoped to individual actions or workflows.
- Clear attribution and auditability for every action performed on behalf of users.
- A standardized approach for securing AI agents across diverse environments and workflows.
These unique operational and security characteristics drove HashiCorp to build new capabilities in Vault specifically for agentic workflows. The result is a suite of features including an agent registry, granular identity-based policies, and per-request authorization controls—all designed to reduce risk by granting temporary access that automatically expires after a specific task or timeframe.
Agent Registry: A New Primitive for Agentic Identities
The agent registry allows developers to register and manage agent activity separately from human and traditional NHIs. This separation is critical, especially in delegation flows where an agent uses an on-behalf-of (OBO) pattern from a human user, complete with delegation and consent. By explicitly tracking such delegations, the agent registry forms the foundation for a dedicated framework that covers registration, authorization, credential management, and observability.
With this new primitive, Vault treats AI agents as first-class entities with their own identity lifecycle. Administrators can see exactly which agents are active, what permissions they hold, and how they are being used—all without conflating agent activity with human or other non-human entities.
Enforcing Granular, Identity-Based Policies
Least-privilege access is a top priority for organizations, and it becomes even more critical when dealing with unpredictable agents. Vault addresses this through rich policy-based runtime controls that strictly govern agent activity. Because agent behavior can be non-deterministic, Vault applies deterministic guardrails and per-request access control to limit the blast radius of any single action.
When agents operate in delegation mode—carrying the authority of a human user—Vault evaluates trust across multiple dimensions. For example, when an agent attempts to access secrets or credentials for target systems, Vault verifies:
- The identity of the agent itself.
- The delegated authority from the human user (with consent).
- The specific context of the current request, including time, location, and resource sensitivity.
This multi-dimensional trust evaluation ensures that agents can only perform actions that are explicitly authorized and directly relevant to their assigned tasks.
Ephemeral Authorization: Per-Request Access Control
One of the most powerful new capabilities is ephemeral authorization. Instead of granting long-lived credentials or permissions, Vault now supports temporary access rights that are tightly scoped to a single request or a short-lived workflow. Once the task is complete—or after a predefined timeframe—the access automatically expires. This dramatically reduces the risk of credential misuse or lateral movement by compromised agents.
Ephemeral authorization is particularly valuable in complex agentic scenarios, such as multi-step workflows where an agent must interact with several services. Each interaction can be authorized independently, with its own expiration window, providing fine-grained control and auditability.
Early Access and Public Beta
Select customers are currently evaluating these capabilities through an early access program. Broader public beta availability is planned for a future Vault release this summer. Feedback from early adopters is already shaping the final design, ensuring that the features meet real-world operational needs.
As organizations continue to integrate AI agents into their core workflows, tools like HashiCorp Vault are evolving to provide the security and governance that these autonomous systems require. By combining agent-specific identity management with runtime policy enforcement and per-request authorization, Vault is helping enterprises embrace agentic AI without compromising on security.
Related Articles
- 10 Essential Features of watchOS 26.5's New Pride Luminance Watch Face You Need to Know
- OpenFactBook: The Free, Community-Run Successor to the CIA World Factbook
- Real-Time AI in Live Video: How AWS Elemental Inference is Changing Media Workflows
- 10 Key Insights into Android's Desktop Mode for 'Googlebook' Laptops
- How to Access and Use the Revamped Windows 11 Run Menu with Dark Mode and the New User Directory Command
- Experts Warn GUARD Act Could Block Teens from Basic Internet Tools, Not Just Dangerous AI
- 10 Ways Donald Trump’s Influence Has Waned in 2026
- The Hidden Giant: Alaska’s 2025 Landslide Tsunami and Its Near-Miss in a Tourist Haven