10 Critical Insights on Ransomware in Q1 2026
Ransomware continues to evolve at a breakneck pace, and the first quarter of 2026 has delivered a fascinating shift in the threat landscape. While attack volumes remain near historic highs, the real story is the unexpected consolidation of power among a handful of dominant groups. Drawing on data from over 70 data leak sites (DLS) that recorded 2,122 victims, this listicle unpacks the key trends, standout players, and structural changes shaping ransomware today. Whether you're a security professional or just tracking the threat, these ten points will bring you up to speed.
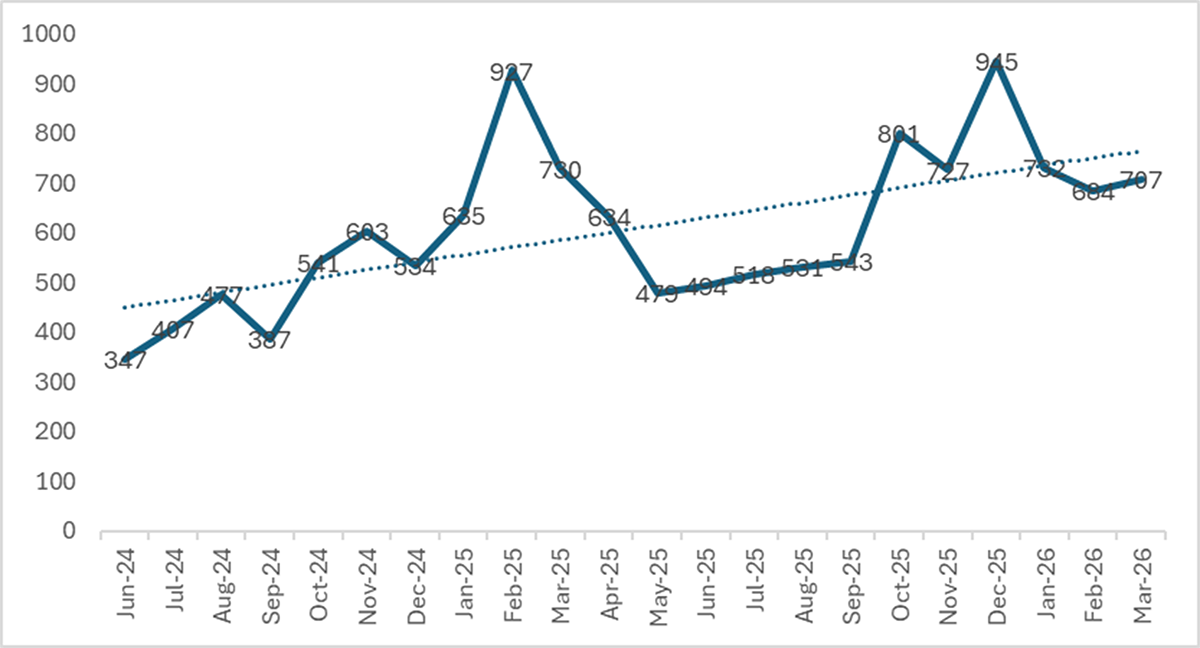
1. Attack Volume Stabilizes at Near-Record Levels
In Q1 2026, analysts logged 2,122 victims on DLS, making it the second-highest first quarter ever recorded. This figure is just 12% below the all-time quarterly record set in Q4 2025 (2,416 victims) and a staggering 117% above Q1 2024 (977 victims). The numbers have leveled off, but they remain elevated, confirming that ransomware operations have adopted a new, higher baseline. Monthly counts were remarkably consistent: 732 in January, 684 in February, and 706 in March—averaging 707 victims per month. This stability suggests attackers have optimized their workflows, operating at a sustainable yet intense pace.

2. Year-over-Year Decline Is Misleading
At first glance, the 7.1% drop from Q1 2025 (2,285 victims) to Q1 2026 looks like progress. But that comparison is skewed by Cl0p’s massive Cleo mass-exploitation campaign in early 2025, which alone added roughly 390 victims. Strip out Cl0p from both periods, and the numbers tell a different story: 1,894 victims in Q1 2025 versus 1,995 in Q1 2026—a 5.3% year-over-year increase. The underlying growth trend in ransomware operations continues, even as spectacular spikes subside. Security teams shouldn't mistake a statistical dip for a real decline in threat activity.
3. Consolidation Reverses Two Years of Fragmentation
The most dramatic structural change in Q1 2026 is the swift consolidation of the ransomware ecosystem. After steadily fragmenting from 51 active groups in Q1 2024 to a peak of 85 in Q3 2025, the number of operators shrank to 71. The top 10 groups now claim 71.1% of all DLS-posted victims—the highest concentration since early 2024. This marks a decisive reversal of the fragmentation trend, which had seen the top-10 share fall from 68% to 57%. The ecosystem is once again coalescing around a few powerful players, raising the stakes for defenders who must track a smaller but more formidable set of adversaries.
4. Qilin Maintains Its Dominance for a Third Quarter
Qilin has solidified its position as the most persistent and prolific ransomware operation, posting 338 victims in Q1 2026. That marks the third consecutive quarter atop the global rankings. The group’s sustained output suggests a mature, well-resourced operation with a broad reach. While other groups rise and fall, Qilin’s consistency makes it a perennial threat. Its victim count alone accounts for about 16% of all DLS activity in the quarter, underscoring the group’s outsize role in the current landscape. Defenders should prioritize understanding Qilin’s tactics, infrastructure, and targeting patterns.
5. The Gentlemen Surges to Third Place
The breakout story of Q1 2026 is The Gentlemen, a group that vaulted from relative obscurity to the global top three. Its victim count exploded from 40 in Q4 2025 to 166 in Q1 2026—a 315% increase. This rapid ascent highlights how new operators can quickly scale using existing tools and leak site infrastructure. The group’s success may reflect a strategic pivot toward targeting mid-sized organizations with weaker defenses, or perhaps a partnership with initial access brokers. Whatever the cause, their trajectory demands close monitoring.
6. LockBit 5.0 Makes a Comeback
LockBit, once the dominant ransomware family, has re-emerged with its 5.0 version, posting 163 victims in Q1 2026—enough for fourth place. This represents a significant recovery after law enforcement disruptions in 2024 and early 2025. The group’s ability to rebuild and re-establish operations shows the resilience of the ransomware ecosystem. LockBit’s return complicates the threat landscape, as it brings a well-known brand, a large affiliate network, and proven encryptors back into active play. Organizations that relaxed defenses against LockBit specific variants should reassess.
7. Fourteen Groups Disappeared, 21 New Ones Appeared
The consolidation wave is not just about the rise of top groups; it also involves a churn in the lower tier. In Q1 2026, 14 groups that were active in Q4 2025 completely vanished from DLS listings, while 21 new names emerged. This turnover suggests a volatile environment where smaller or less successful operations either disband, rebrand, or get absorbed. The overall reduction from 85 to 71 active groups indicates that the ecosystem is winnowing out weaker players, concentrating victim volume among those with proven capabilities.
8. Monthly Volumes Show Remarkable Stability
Unlike previous periods marked by feast-or-famine patterns, Q1 2026 exhibited steady monthly victim counts: 732, 684, and 706. This stability implies that ransomware operators have standardized their methods, perhaps using automated tools or consistent affiliate pipelines. The lack of large spikes also suggests that mass-exploitation events (like Cl0p’s Cleo campaign) are becoming less common—or that defenders are quicker to patch critical vulnerabilities. For incident responders, this predictable cadence can help allocate resources more efficiently, but it also means adversaries are operating a well-oiled machine.
9. Two-Thirds of Victims Sit Outside the Top 10
Even with consolidation, roughly 29% of victims are posted by groups outside the top 10. This long tail of smaller operators continues to pose a threat, especially to niche industries or regions. While the big players grab headlines, numerous mid-size and small ransomware groups still account for hundreds of attacks per quarter. Their lower profile can make them harder to track, and they often target organizations that lack the resources to defend against high-end threats. Security strategies must account for both the giant and the swarm.
10. The Underlying Growth Trend Persists
When you remove the distorting effect of Cl0p’s campaign, the adjusted victim count shows a 5.3% year-over-year increase for Q1 2026. This indicates that, beneath the surface, ransomware activity is still expanding. The consolidation of top operators may actually accelerate growth by creating more efficient criminal enterprises. As groups like Qilin, The Gentlemen, and LockBit compete for victims, they invest in better tools, more effective extortion tactics, and broader targeting. The long-term trajectory points upward, even if quarterly fluctuations obscure the trend.
Understanding ransomware in Q1 2026 means looking beyond the numbers to the structural shifts. Consolidation, the emergence of new players, and the persistence of high-volume operations all point to an adaptive and resilient threat ecosystem. For defenders, this is a call to stay vigilant, invest in threat intelligence, and prepare for a future where the top groups only grow stronger. The ransomware battle is not a short sprint—it’s an enduring marathon with no finish line in sight.
Related Articles
- Expanding Video World Models: How State-Space Models Unlock Long-Term Memory
- 10 Media Milestones: How Artemis 2 Astronauts Became Overnight Stars
- MIT Unveils Virtual Violin That Simulates Acoustic Physics to Aid Luthiers
- Witness a Celestial Triangle: Mars, Saturn, and the Moon Align Before Dawn on May 14
- Soyuz 5 Rocket Successfully Completes Maiden Flight: A Milestone for Russian Space Program
- AI-Generated Content on the Rise: Stanford Research Quantifies the 'Dead Internet' Theory
- Rethinking Reality: Could Consciousness Be More Fundamental Than Quantum Physics?
- Orbital AI Data Centers: A Comprehensive Guide to Launching Edge Computing in Space